Darknet marketplace vendors sell of some truly unique items. They offer, of course, plenty of ‘get rich quick’ schemes and services such as the one below. This ad is for a sports betting tipping service. It was posted by someone who has “connections with top tipsters on the world” and that specializes in “EU / Worldwide Soccer”. According to its numerous feedbacks, anyone can make a quick 40% profit and win every time! What a deal.
Sport betting advertisement

Should sport betting not be your thing, you can always try your hand at buying antiques from either the Roman empire or Egyptian pharaohs era. This vendor can apparently also supply his buyers with “animal skeletons” (fossils perhaps?). He will also ship to anywhere in the world! The perfect gift for that special someone who has everything.
Antiques advertisement
While entertaining, ads like these only represent a tiny fraction of the ads posted on the darknet. We have witnessed over the past years a large increase in the use of the darknet to buy and sell stolen financial information. When facilitated by the darknet, financial fraud is usually a labour that is divided into two or three steps.
Steps of financial fraud
In the first, an offender steals financial information from various sources. These can be physical (ex. stealing mail containing financial information) or virtual (ex. infecting a point of sale system). Once acquired, this stolen financial information is either sold to a wholesaler (second step) or to a fraudster (third step). These offenders use the stolen financial information to make purchases online or in stores. These purchases are then sold on the grey or black market for cash.
Flare Systems Inc. has been monitoring the darknet for ads that offer stolen financial information and has come to two realizations over the past month. First, the supply side of stolen financial information may be more concentrated. Second, the targets of the theft of financial information tend to change from month to month significantly.
Concentration of the supply side of stolen financial information markets
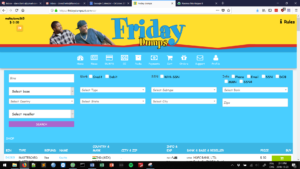
Monitoring the sale of stolen financial information on the darknet was at first a tedious task for us. Many websites advertise stolen financial information in online shops. These shops allow their customers to make very specific queries. These queries are about the types of cards that they wish to purchase as demonstrated in the image below. Customers search for credit and/or debit card. They also select an issuing bank, country or even city of activity of the victim. All the online shops selling stolen financial information have unique looks and feels. This means that data collection tools must be customized for each website.
Carding website
While probing the network traffic between our systems and the online shops, our team figured out that the websites were making API queries rather than load data from a database. While comparing notes over many days of work, our team members realized that many of the largest online shops used the same API. The only difference between the online shops was the URL of the website.
This points to two conclusions. Either a single actor (or group of actors) is facilitating a large portion of the sale of stolen financial information on the darknet or many actors (or group of actors) are buying the same website from a coder to host their online shops. At this point, it is not possible to rule out an option. It raises however some interesting question about the concentration of the supply side of stolen financial information markets. Indeed, the vulnerability to disruption of these markets would be very high if a small number of actors facilitate a large portion of the sales.
Targets of the theft of financial information
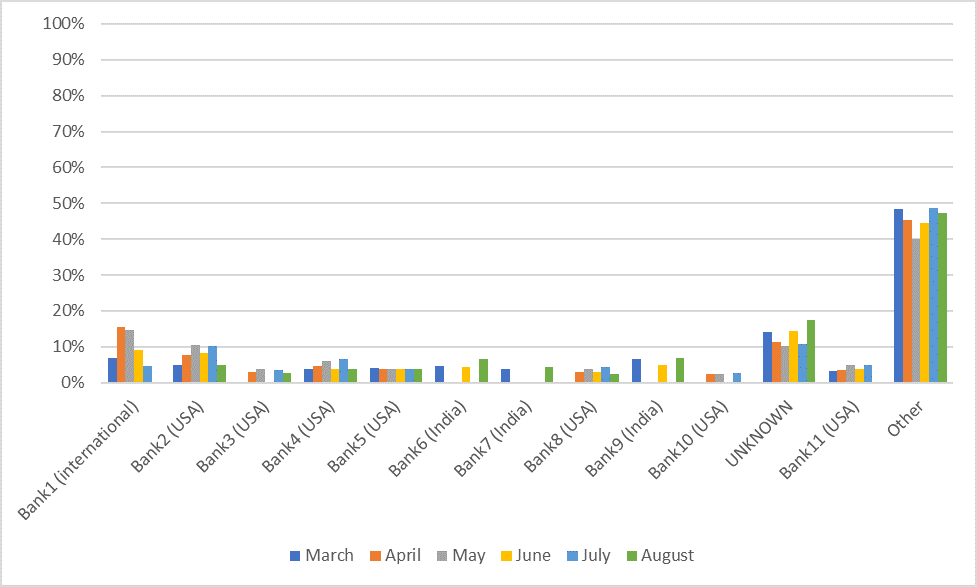
Another interesting take away from our daily monitoring is the changes in the victims of financial fraud. We extracted for a single online shop the names of the banks of the credit cards that were for sale. We aggregated those on a monthly basis between March and August of 2018. The figure below presents the share of cards for the 13 most victimized institutions. Each bar represents a month of data.
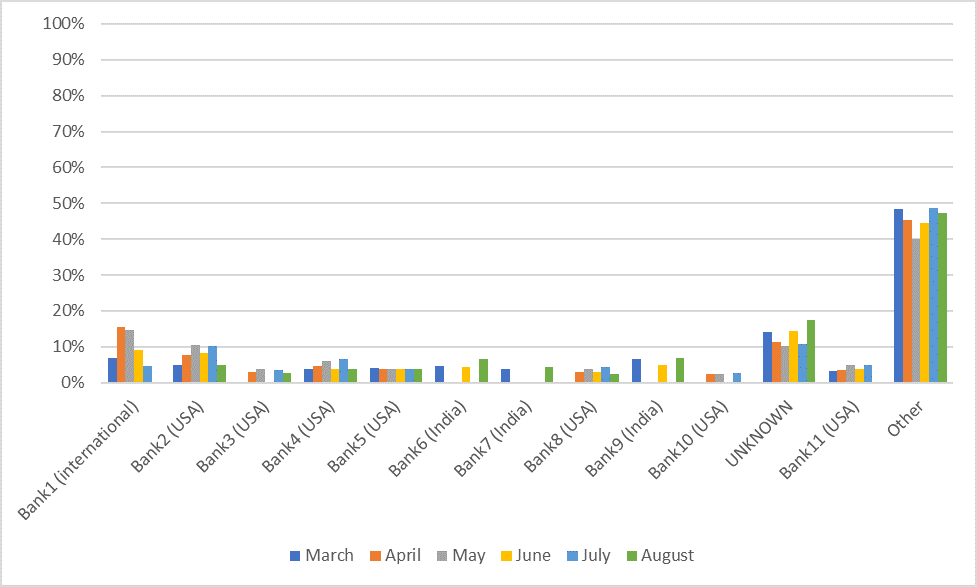
This figure shows that these 13 financial institutions, while representing perhaps 0.1% of all financial institutions in the world, account for about half of all the cards offered on darknet online shops. This suggests that fraudsters have developed strategies to target specific institutions in India and the United States for the most part.
For some of these institutions, there does not appear to be significant variations. Bank 5 is not more or less victimized over time and represents 4% of all cards sold. Bank1 tells a very different story. It was responsible for between 3% (August) and 15% (April) of all cards offered on the online shop.
The coefficient of variation is often used to measure the variations of metrics over time. To calculate it, we divide the standard deviation of a dataset by its mean. In this case, this coefficient varies for each bank between 3% and 42% with an average of 17%. This level of variation is not considered high. It is significant enough though to demonstrate that the activities of fraudsters does change over time. Institutions that were once targeted may not be as much for a certain period only to come back a few months later.
Take-aways
This finding stresses the need for financial institutions to constantly monitor the evolution of the supply side of stolen financial information on the darknet. By taking a snapshot of darknet activity, it would be easy for a financial institution to either build a false sense of security. It could also invest too many resources in a problem that is declining over time (see the last five months of Bank1 for example).
Ongoing monitoring of darknet sales also has the advantage to derive hard numbers on the state of the industry. This helps financial institutions to evaluate the impact of their actions on the number of their customers’ financial information being sold online. A prevention campaign should lead to lower numbers and the constant monitoring that Flare Systems Inc. offers will help financial institution understand what their exposure is.
Flare Systems Inc.’s data is therefore very useful to understand threats against financial institution. In a next blog post, we will also demonstrate how this information can be used to understand many social transformations such as the legalization of cannabis in Canada!
Subscribe to our blog to stay up to date on darknet and cybersecurity.