Building cyber threat intelligence capabilities has never been more important than in 2021. Attacks against businesses of all sizes are increasing rapidly. At the same time, the criminal underground is larger and more differentiated than ever. A single cyberattack against a business might involve dozens of threat actors each performing highly specialized roles.
Gaining visibility into the dark web is a critical component of digital risk protection. Deep and dark web forums are a rich source of threat intelligence. Identifying leaked account credentials can provide the opportunity for your organization to identify potential cyberattacks before they happen, and allow you the opportunity to prevent them.
What Is Threat Intelligence?
Threat intelligence is the knowledge and tooling that enables organizations to understand the cyber threat landscape, and prevent or mitigate attacks to their networks, systems, or applications using data collection.
Threat intelligence is not simply data. Rather, it is contextual data that can help you make informed security decisions by understanding more about:
- The attacker
- Their motivation
- Their capabilities
- Their attack behaviors
- Potential Indicators of Compromise (IoC) you should look out for
By leveraging threat intelligence, you can proactively fight threat actors and data breaches, and enable your security teams to even get ahead of them.
Threat Intelligence on the Dark Web
The Dark Web is characterized by its anonymity and hidden nature. Cybercriminals regularly sell massive amounts of stolen data on it, including login credentials, proprietary code, and intellectual property. In 2020, over 18 billion raw identity records passed through the Dark Web. All a buyer needs is a Tor browser and some Bitcoin, and they can start “shopping” right away.
While these are huge cybersecurity concerns for organizations, they can also empower your organization to extract threat intelligence. By monitoring these dark web sources, you can understand the latest threats, place them in the context of your own cybersecurity infrastructure, and take proactive action to strengthen them.
Types of Threat Intelligence on the Dark Web
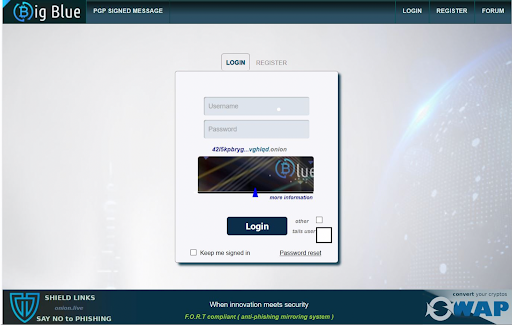
You can find many different types of threat intelligence to discover, detect and prevent threats. In many cases, threat intelligence may be hidden on marketplaces behind authentication requirements. Using specialized dark web threat intelligence tools can make it easy since in many cases they already have access to gated marketplaces.
Targeted Attacks
In some cases threat actors will discuss targeted attacks against specific individuals and organizations on dark web forums and marketplaces. These conversations can provide valuable insight into potential attack vectors as well as to inform your risk management team.
Exposed Credentials
In 2020, the credentials of almost 134K C-level Fortune 1000 executives were exposed on the Dark Web, along with over 543 million employee credentials. In June 2021, an entity uploaded 100GB of stolen and leaked passwords containing 8.4 billion entries to a Dark Web user forum.
Credentials are extremely valuable on the Dark Web, allowing cybercriminals to use them to carry out the profitable credential stuffing and Account Takeover (ATO) attacks.
Value as Threat Intelligence: Use this information to strengthen your password policies, educate users on the perils of using weak or common passwords, and strengthen your access infrastructure with Multi-factor Authentication (MFA).
Vulnerability Information
Every application has vulnerabilities that can be exploited by cybercriminals. Open-source software is particularly at risk. In 2020, 94% of projects were found to rely on open-source components, which can result in additional risk. Zero-day vulnerabilities are especially rampant on the Dark Web. Since security patches do not yet exist for these flaws, threat actors can leverage them to attack companies.
Value as Threat Intelligence: Information on these vulnerabilities can help you identify the gaps in your software, implement effective controls to prevent an attack, and fix the gaps as soon as the patch is released.
Insider Threats
Insider threats are a huge cybersecurity risk to your organization, whether they originate from current or former employees, vendors, partners, or resellers.
Value as Threat Intelligence: The Dark Web is a rich source of information about insider threats, and insiders looking to sell your company’s trade secrets, intellectual property, or sensitive data. Monitor paste sites, underground marketplaces and user forums for your organization’s name. If it appears, investigate the insider threat, and take action to mitigate it before it leads to an access breach, data leak, or a cyber extortion attempt.
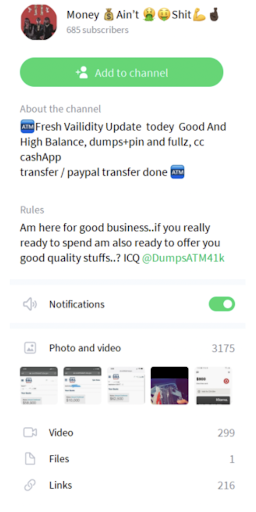
Hacked Accounts
Buyers and sellers on the Dark Web interact directly to share information about different types of user accounts, including email, bank accounts, eCommerce sites, and social media. Company databases containing sensitive information about employee accounts, partnerships, contracts, M&A deals, etc. also frequently appear.
Value as Threat Intelligence: Information about hacked accounts is also valuable threat intelligence that can help you strengthen your security profile. Regularly scan the Dark Web to check if your company name, account details, or database appears on a marketplace or messaging app. If it does, act immediately to ensure the information cannot be used to exploit or extort your organization.
According to our research, effective spear-phishing accounts for up to 95% of attacks targeting business networks. Users open 30 percent of phishing emails, with 12 percent of those who are targeted clicking on the malicious link or file. According to the data, one out of every eight employees provides sensitive information on a phishing site, with a single spearphishing assault costing an average of $1.6 million.
Botnets for Sale
Stolen credentials, source code, and payment information isn’t all that is for sale on the dark web. Some malicious actors have built up massive networks of zombie computers that can be rented or bought, and used to launch cyberattacks such as distributed denial of service, bank fraud, and spam. Individual bots can be purchased for less than $100.
In addition, botnets can help threat actors launch attacks anonymously without as much risk of being traced back to a specific source, reducing risk for the attacker. Botnet sellers have become so sophisticated that they’ve created plugins that would-be attackers can download onto their browser to mimic the fingerprint of other users.
How to Find Threat Intelligence on the Dark Web
The best way to extract threat intelligence from the Dark Web is via a monitoring service from a specialized vendor. Flare offers an easy to use digital risk protection tool that enables you to leverage threat intelligence without the need for a specialized staff.
The other option is to monitor the Dark Web on your own. The upside of this approach is that you can tailor the search for your specific needs. However, the Dark Web is not indexed by Google and other search engines. Therefore, it can be difficult to navigate and find actionable threat intelligence. Moreover, aimless browsing can be dangerous for inexpert users.
If you still prefer this route, here are some tips to guide you (caution recommended!):
- To find Dark sites, find references on directories, boards or forums
- Only look at sites that can potentially yield relevant threat intelligence, e.g. posts or forum discussions
- Avoid any action or search terms that could identify your organization or you as an individual. Using a platform like Flare can help by conducting searches on offline cached copies of dark web sites.
- Review Dark Web Links, Onionscan, or Onion Past to find website links
- Use the Ahmia search engine to find Dark sites
- Look for threat intelligence:
o The Hidden Wiki: The Dark Web’s Wikipedia
o PwDB: Password database
o Dread: The Dark Web’s Reddit
Automated Dark Web Threat Intelligence
Contextual, actionable threat intelligence is crucial for your organization’s safety. The Dark Web offers many opportunities to extract this intelligence, and use it to identify, profile, and mitigate cybersecurity risks. If used right, it can be a powerful addition to your security ecosystem, and defeat threat actors at their own game. The process of data collection, refinement, and threat hunting can be time-consuming without the right team or tools.
The Dark Web shouldn’t be your only concern though. While it can be tempting to focus all threat intelligence resources at dark web monitoring specifically, monitoring the clear and deep web can also provide enormous value to organizations. Threat actors regularly post leaked credentials to pastebin and other services.
Flare Systems provides an easy to use tool that works in minutes to find actionable threat intelligence on both the dark and deep web. Using a digital risk protection platform to quickly sort through noise and identify threats that pose a risk to your organization can dramatically expand your cybersecurity capabilities at little cost.



