For anyone trying to collect data on the darknet, the last three years have been an incredible challenge. The dark net used to be a collection of simple marketplaces that could be easily indexed and crawled, though sometimes slowly because of the size of some of the markets. Alpha Bay, for example, had an estimated 200,000 users as well as 350,000 listings when it was taken down by law enforcement in 2017.
Technical issues with the Tor network
It is easy to forget that the Tor network is not some sophisticated network run by a large corporation with high service-level agreement. Rather, it is a relatively small network – by today’s standards – that is run by a small group of individuals with limited means. The network is constantly under attack, with recent reports mentioning that a sustained attack had made some of its websites unavailable.
This is not the first time that the Tor network is under attack. A few years ago, the Tor Project claimed that a group had been paid by the F.B.I. to infiltrate the network and unmask the identity of its users. Whether these attacks are coming from malicious actors or law enforcement, these disruptions make it harder for users to connect to the network, and for website hosters to anonymously host their webpages.
Denial of service attacks
In addition to attacks that target the network itself, the darknet has been the host of frequent and intense distributed denial of service attacks (DDoS). No one knows exactly who is responsible.
In response, dark net market administrators have started to create unique domain names for each of their vendors to at least enable them to log in to the platform and deal with their sales. Recent discussions though on forums suggest that darknet marketplace administrators are behind some of the DDoS attacks, as they try to make the user experience on their competitors’ platforms as poor as possible.
DDoS can be expensive to launch, but since administrators take a commission on each transaction on their platform, convincing a few wealthy buyers to switch to their platforms can quickly repay the costs of any DDoS.
Usurpation of the identity… of darknet marketplaces
Another significant challenge to data collection – and the use of darknet marketplaces for illicit activities – is the rise of fake mirror websites. A 2020 study found that over half of all available darknet marketplaces were imitations of real markets. This makes the task of finding the real darknet marketplaces quite difficult.
The motivation to create fake marketplaces is clear. Lured victims will try their usernames and passwords which can be reused on the real website to steal the victims’ cryptocurrency holdings on that market. Victims will also make purchases and send their bitcoins to the fake website, with no real vendors.
This is also a significant problem for data collectors who may be indexing old and dated fake mirror websites rather than the real ones. This reduces the quality of the data collected, and even risks creating new risks that are not based on any real activity. Malicious actors could for example put up for sale a new malware at a discounted price to make sales, but never indeed have access to that malware.
The darknet is more constrained than ever
The net results of all these issues is that the darknet is, and has been for quite some time, struggling to grow. The chart below shows the revenues of all darknet marketplaces over the past 6 years based on an analysis by Chainalysis.
The chart clearly suggests that the dark web is growing in size, but only because of a single Russian marketplace, Hydra, which has become the de facto distribution channel for illicit drugs and much more in Russia and some neighboring states.
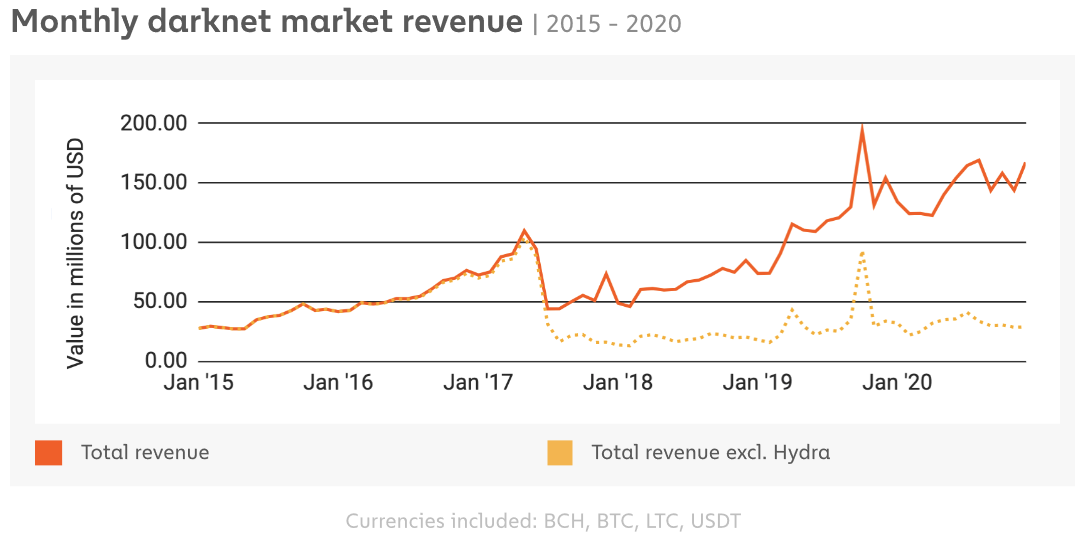
The dotted yellow line represents the transactions for all other markets combined. We see that after the take down of Alpha Bay, things were never quite the same and that the sales have been mostly flat ever since.
There are many hypotheses we can pose to explain the sudden drop, and flatten of the curve here. Today we discussed many issues that make the dark net very impractical for its users. It is therefore no surprise to see that these same users are looking for alternatives to the dark net.
There have been hypotheses that these would be decentralized platforms such as Tor Bazaar and I2P, but nothing has as of yet taken over the expected growth of the dark net. The best explanation is that much of the activity has shifted to the internet, and chat messaging systems hosted in Russia such as Telegram and ICQ.
There has also been mentions of Discord as a facilitator of communications for illicit communities, but with the upcoming purchase of the service by Microsoft, it is very likely that illicit activities will be censored by Microsoft in the coming years.
Does this mean that you should not look into the darknet to detect and prevent risks to your organizations? Of course not. It does however better situate where your risks are likely to come from, and to demonstrate that a good digital risk protection strategy includes the dark net, but also many other communication channels that may not be as private, but may be much more popular. It also suggests that users are aware of the issues of anonymous networks, and that they may shift away from them when they are confronted with practical problems, just as they may shift to them when the regulation of the internet becomes too intense.