Over the past decade, the dark web has attracted much of the attention in the security field as the premier source of threats for companies. Our years of monitoring the dark web have helped better understand what it is, and most importantly, is not.
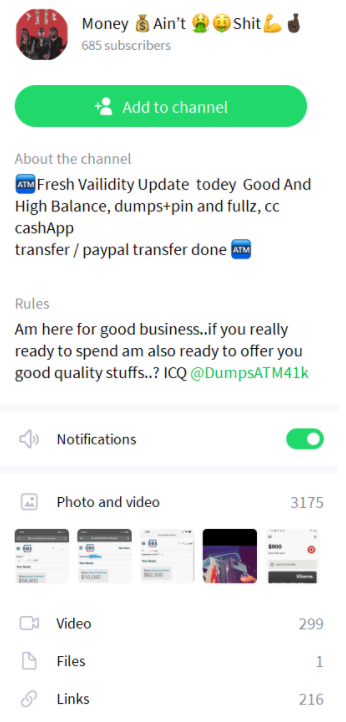
The dark web is host to many dynamic malicious actor communities. These communities have however been the target of several police operations and, coupled with the technical challenges of using the dark web, there have been growing signs that the most dynamic communities are now hosted on chat rooms on Discord, Telegram and ICQ.
There is still much uncertainty around what these chat rooms are, and are not. The aim of this blog post is to help you get a better grasp as to how chat rooms are used, and why your company should pay attention to them. For the benefit of our demonstration, we will use the ICQ network.
ICQ, back from the dead
I used ICQ back in the 1990s during my high school years to keep in touch with my friends. The network went underground for a number of years, and was resuscitated by a Russian company. Being hosted in Russia, Western law enforcement receive little to no cooperation from its operators when sending mutual legal assistance treaty (MLAT) letters, and warrants. ICQ participants operate therefore with a certain sense of anonymity, and impunity.
ICQ provides the ability to search for participants by name, and to exchange private messages. ICQ also has chat rooms where up to thousands of participants converge. Chat rooms can be public or private, and share text as well as images, videos, files and audio recordings.
Channel hopping makes it difficult to keep track of the criminal underground
There are thousands of chat rooms involved in various criminal activities. Some are extremely large, while others only have a few dozen members. Finding these chat rooms is difficult because ICQ does not offer a universal search engine. Instead, users must find links to chat rooms, and click on them to join the rooms.
Another challenge is that many chat rooms are private, meaning moderators must accept new join requests. Joining these rooms requires infiltration, and the creation of fake, credible online profiles.
Finally, malicious actors tend to move from one channel to another regularly. Actors will announce that they are moving to a new channel, often adding v2, v3, v4… to the name of their channels. Bots that are not configured to join new chat rooms automatically will be left behind, and unable to collect messages from the ongoing conversations.
ICQ is a provider of actionable intelligence
Perhaps one of their most valuable roles is their ability to source actionable intelligence on victims. Malicious actors are unable to create profiles on ICQ, and to establish their credibility through a history of messages. ICQ makes it decidedly difficult to find past messages of a user.
As a result, malicious actors cannot simply claim to “have hacked into the backend of a company” to find business partners willing to purchase the data they stole. They must provide proof, evidence of their crime. This can be a screenshot that often contains the name of the victim, its account number and institution.
On the dark web, malicious actors are able to build credible profiles, and to share links to their reputation score and past activity. This means that they rarely post actionable intelligence. Chat rooms therefore provide more specific information that is not found anywhere else.
ICQ helps to profile victims
Most messages on chat rooms are for products and services for sale, or products and services that are needed. These messages are short, direct, to the point. They do not provide any information about who the malicious actor is, but leaves little doubt about who their target is.
This is very valuable information to draw statistics on whom is targeted by malicious actors, and how that evolves through time. It is possible to find mentions of CVE, institutions that have been hacked and to predict who is currently most targeted. This can help build a risk profile for institutions to understand if they, or their industry, is under sustained attack.
ICQ is not helpful for identification
With the majority of communications being about the products and services, there is little room on ICQ for personal discussions, or even discussions of tactics and methods. Yes, malicious actors may share whom they have hacked; they will not post tips about how they managed to do it, unfortunately. This means that social profiling, and identification of participants is unlikely, if relying only on public messages on chat rooms. Some private rooms have flashes of discussions, but most rooms should be understood as streams of publicity.
ICQ is fragmented based on origin, illicit activity
With thousands of chat rooms active at any moment, it is important to understand that malicious actors seek rooms where they are likely to find like-minded people. This is why many chat rooms have icons of flags in their names to identify to which country their members belong. Most chat rooms are also dedicated to a single type of offense rather than a general hacking, or fraud channel.
This entails that to collect the best intelligence, it is essential to identify the chat rooms that are likely to target you, and to monitor its links to find connections to other similar rooms. Chat room participants can easily be active in tens of chat rooms at the same time.
Conclusion
Perhaps the most valuable aspect of chat rooms is that they provide a great proximity to a large number of malicious actors. This means that it is easy to engage malicious actors, and learn more about their tactics and methods through private communications.
This is where malicious actors draw the most value from chat rooms. They post ads about their products and services, and then negotiate the details of the transaction in private. This access to malicious actors means that it is not as necessary to go through intermediaries, and this levels the playing field of collecting intelligence on malicious actors.
Chat rooms often contain screenshots of deals gone wrong, and this highlights the risky nature of chat room transactions. The dark web uses escrow systems, cryptocurrencies and trusted third parties to protect against internal fraud. Chat rooms are not as sophisticated, and while easier to use, they also are more prone to fraud.
Still, chat rooms are dynamic settings well worth your time and energy to monitor. The main challenge is finding the chat rooms where malicious actors are targeting you.